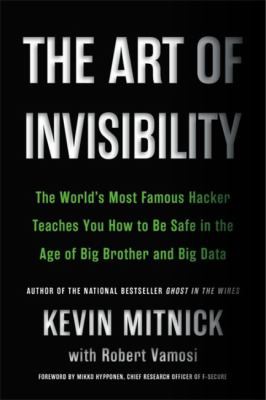
The Art of Invisibility: The World's Most Famous Hacker Teaches You How to Be Safe in the Age of Big Brother and Big Data
"Whenever you write an e-mail, no matter how inconsequential, and even if you delete it from your inbox, remember that there's an excellent chance that a copy of those words and images will be scanned and will live on—maybe not forever, but for a good long while."
The world's most famous hacker teaches practical privacy techniques to protect personal data from corporate tracking and government surveillance. Mitnick draws on decades of experience to guide readers through real-world security threats and actionable countermeasures for the digital age.
This book bridges the gap between hacker mindset and defensive security, showing how attackers think and exploit human behavior. Essential for understanding privacy as a fundamental right and learning practical techniques to maintain digital invisibility in an increasingly surveilled world.
- Encryption is essential for protecting communications from surveillance and interception
- Social engineering remains one of the most effective attack vectors because people are more vulnerable than systems
- Privacy requires constant vigilance and proactive measures in the digital world
- Understanding attacker psychology helps develop more effective defensive strategies
- Some techniques described may be outdated as privacy tools and threat landscapes evolve quickly
- Primarily focused on defensive measures rather than explaining underlying technical mechanisms
"Kevin's book is the must read in this new world."
Steve Wozniak, Apple Co-founder"Who better than Mitnick—internationally wanted hacker turned Fortune 500 security consultant—to teach you how to keep your data safe?"
Esquire Magazine, Media Publication